MTU (IPv4) tests in Linux
I noticed I have several networks with all ICMP messages blocked at the firewall level, except for ICMP echo and reply.
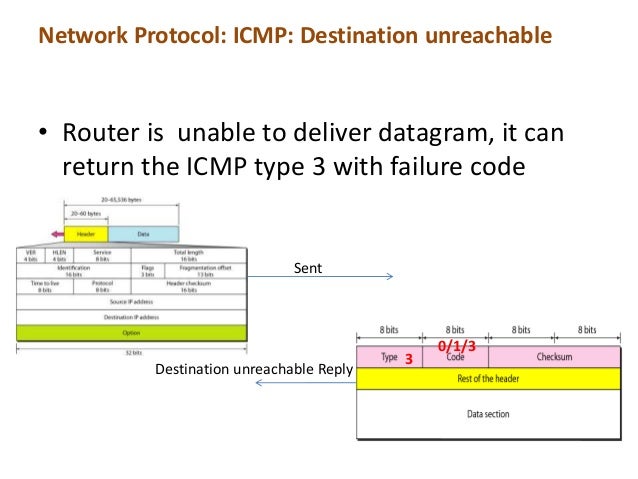
I know that there is a need at least ICMP messages type 3 in IPv4 have to be allowed for the MTU negotiation to occur.
The packets can be sniffed with the command:
sudo tcpdump icmp
However, how do I generate ICMP packets type 3 on one remote point to make global tests?
You need ICMP type 3 "destination unreachable" packets to provide healthy IP connections.
The easiest way to generate ICMP packets type 3 for testing is by using the nping program.
The nping program is part of the nmap package, and as such there is a need to have it installed. For it you have to do:
sudo apt install nmap
After having it installed, to test a remote Linux system, starting running on the remote side, to listen for ICMP type 3 and 4 packets:
sudo tcpdump 'icmp[0] = 3'
or
sudo tcpdump '(icmp[0] = 3) and (host ip_or_dns_of_nping_sender)'
and then do the other system/side to send the ICMP type 3 packets:
sudo nping --icmp-type 3 ip_or_dns_of_remote
Be sure to test them in both directions.
As an example, using the loopback interface to show the test in the local machine:
In the first terminal - listening for ICMP type 3 messages:
$sudo tcpdump -i lo 'icmp[0] = 3'
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on lo, link-type EN10MB (Ethernet), capture size 262144 bytes
21:37:44.089420 IP localhost > localhost: [|icmp]
21:37:45.090092 IP localhost > localhost: [|icmp]
21:37:46.091289 IP localhost > localhost: [|icmp]
21:37:47.093095 IP localhost > localhost: [|icmp]
21:37:48.095019 IP localhost > localhost: [|icmp]
^C
5 packets captured
10 packets received by filter
0 packets dropped by kernel
In the second terminal - sending ICMP type 3 messages:
$sudo nping --icmp-type 3 localhost
Starting Nping 0.6.47 ( http://nmap.org/nping ) at 2017-03-06 21:37 WET
SENT (0.0221s) ICMP 127.0.0.1 > 127.0.0.1 Destination unreachable (type=3/code=0) ttl=64 id=40477 iplen=28
RCVD (0.2088s) ICMP 127.0.0.1 > 127.0.0.1 Destination unreachable (type=3/code=0) ttl=64 id=40477 iplen=28
SENT (1.0228s) ICMP 127.0.0.1 > 127.0.0.1 Destination unreachable (type=3/code=0) ttl=64 id=40477 iplen=28
RCVD (1.2088s) ICMP 127.0.0.1 > 127.0.0.1 Destination unreachable (type=3/code=0) ttl=64 id=40477 iplen=28
SENT (2.0240s) ICMP 127.0.0.1 > 127.0.0.1 Destination unreachable (type=3/code=0) ttl=64 id=40477 iplen=28
RCVD (2.2088s) ICMP 127.0.0.1 > 127.0.0.1 Destination unreachable (type=3/code=0) ttl=64 id=40477 iplen=28
SENT (3.0258s) ICMP 127.0.0.1 > 127.0.0.1 Destination unreachable (type=3/code=0) ttl=64 id=40477 iplen=28
RCVD (3.2088s) ICMP 127.0.0.1 > 127.0.0.1 Destination unreachable (type=3/code=0) ttl=64 id=40477 iplen=28
SENT (4.0277s) ICMP 127.0.0.1 > 127.0.0.1 Destination unreachable (type=3/code=0) ttl=64 id=40477 iplen=28
RCVD (4.2088s) ICMP 127.0.0.1 > 127.0.0.1 Destination unreachable (type=3/code=0) ttl=64 id=40477 iplen=28
Max rtt: 186.715ms | Min rtt: 181.081ms | Avg rtt: 184.307ms
Raw packets sent: 5 (140B) | Rcvd: 5 (140B) | Lost: 0 (0.00%)
Nping done: 1 IP address pinged in 4.24 seconds
Collected from the Internet
Please contact [email protected] to delete if infringement.
Related
Related Related
- 1
Access IPV4 address of local linux machine
- 2
How to compile only net/ipv4 of Linux Kernel?
- 3
Definition of 'send_redirect' in Linux IPv4 context
- 4
Linux networking: Split eth0 (w/multiple ipv4) giving each ipv4 its own virtualdevice and namespace
- 5
Linux netstat shows ipv4 mapped ipv6 address
- 6
Linux kernel IPv4 and IPv6 socket creation: EPROTONOSUPPORT and ESOCKTNOSUPPORT errors
- 7
Why are linux's IPv4 address taking 16 bytes instead of 4
- 8
Linux: in6addr_any and bind to specific IPv4 address
- 9
IPSET matching unavailable for one linux installation, but not another... and only IPv4 is affected
- 10
When does Linux use publicly routable IPv4 address configured on a loopback interface?
- 11
Is there a way to programmatically set an interface MTU using C in Linux?
- 12
How can a small MTU cause a Linux kernel crash?
- 13
In linux does "/proc/sys/net/ipv4/tcp_keepalive_time" has impact on both client & server?
- 14
How to access internet which requires manual IPv4 settings and LDAP-username-password login during Arch Linux installation?
- 15
Linux Networking: How to forward incoming IPv6 connections from the internet via a second IPv4 interface to other computers in a local network?
- 16
Is there a way in linux to increase the MTU size of a Broadcast interface on linux to be able to send bigger UDP packets?
- 17
Service fabric and IPv4
- 18
Broadcast address in IPV4
- 19
IPv4 changes by itself
- 20
Disable IPv4 completely?
- 21
What is the IPV4 class ?
- 22
Access IPV6 with IPV4
- 23
Access IPV6 with IPV4
- 24
IPv4, IPv6 and IPTables
- 25
Automated tests with TFS for Linux systems
- 26
Linux - net.ipv4.conf.all
- 27
In TSPC IPv6 tunneling, is a tunnel broker required for IPv4 to IPv4 communication?
- 28
IPv4 is not getting configured on Ubuntu in a dualstack (IPv4/IPv6) network
- 29
Making IPv4 request IP use IPv4 notation instead of IPv6
Comments